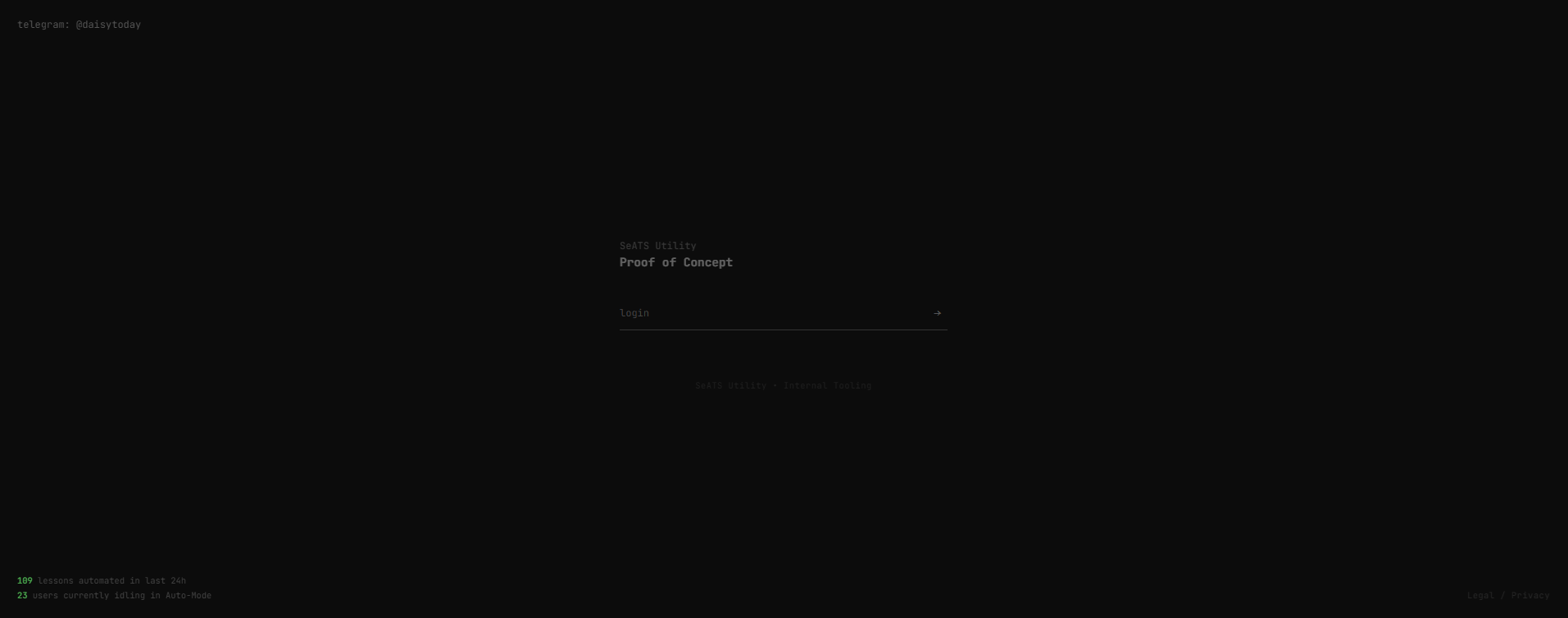
Technical deep-dive into the architectural failures of the SeATS student ecosystem. v2.1.0 is a hardened, private Proof of Concept demonstrating the risks of persistent session hijacking within their mobile API.
SeATS relies on a flawed OAuth implementation via 01v2mobileapi. Persistent session tokens and a lack of server-side validation make identity hijacking trivial once a Bearer token is leaked.
| PHASE | OPERATION | METHOD |
|---|---|---|
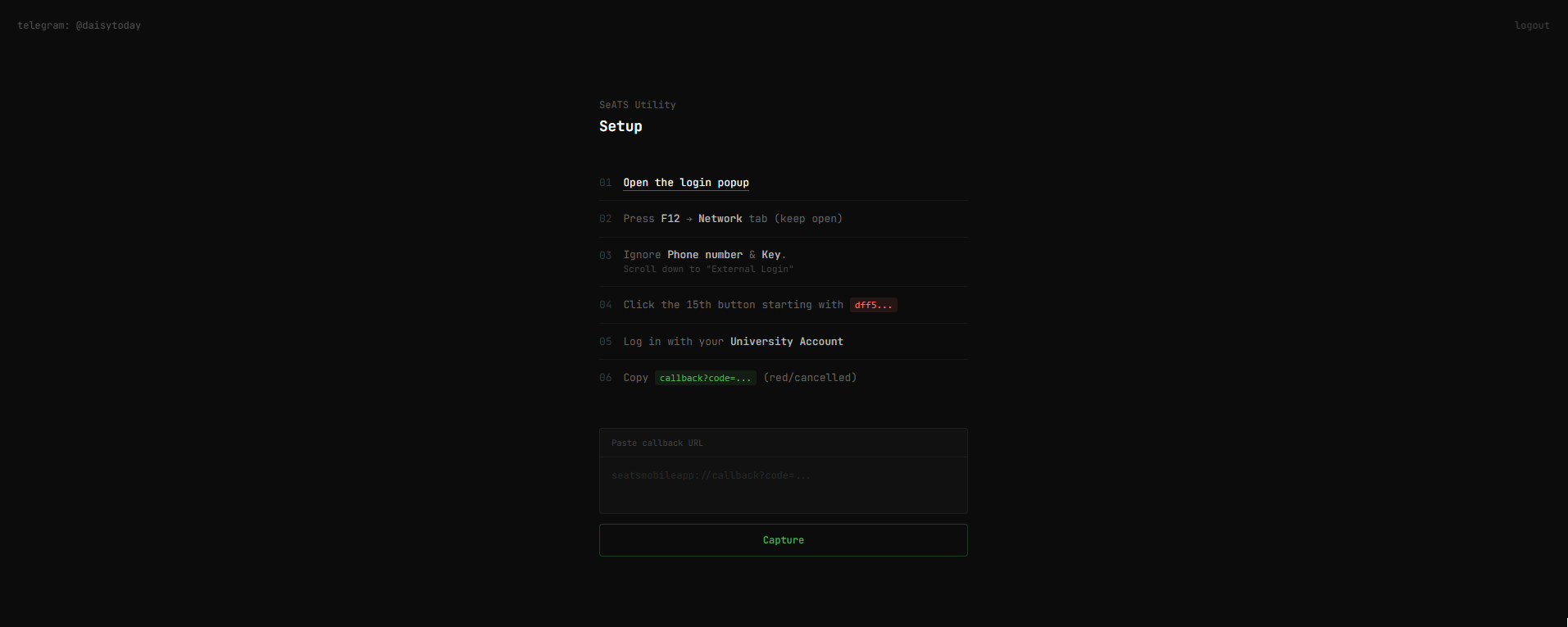
| 01 | Handshake | Trigger standard OAuth flow in sandboxed popup. |
| 02 | Interception | Catch callback via DevTools (bypass desktop URI restrictions). |
| 03 | Injection | Token swallowed by server-side scheduler (±60s jitter). |
This exploit has been public for over 12 months. Despite direct reports sent to the SeATS Team, the structural flaws in the mobile API remain unpatched. This build serves as a live reminder that client-side trust in an OAuth handshake is a fundamental architectural error.
The private build is a full-stack Node/Express implementation focused on Identity Masking:
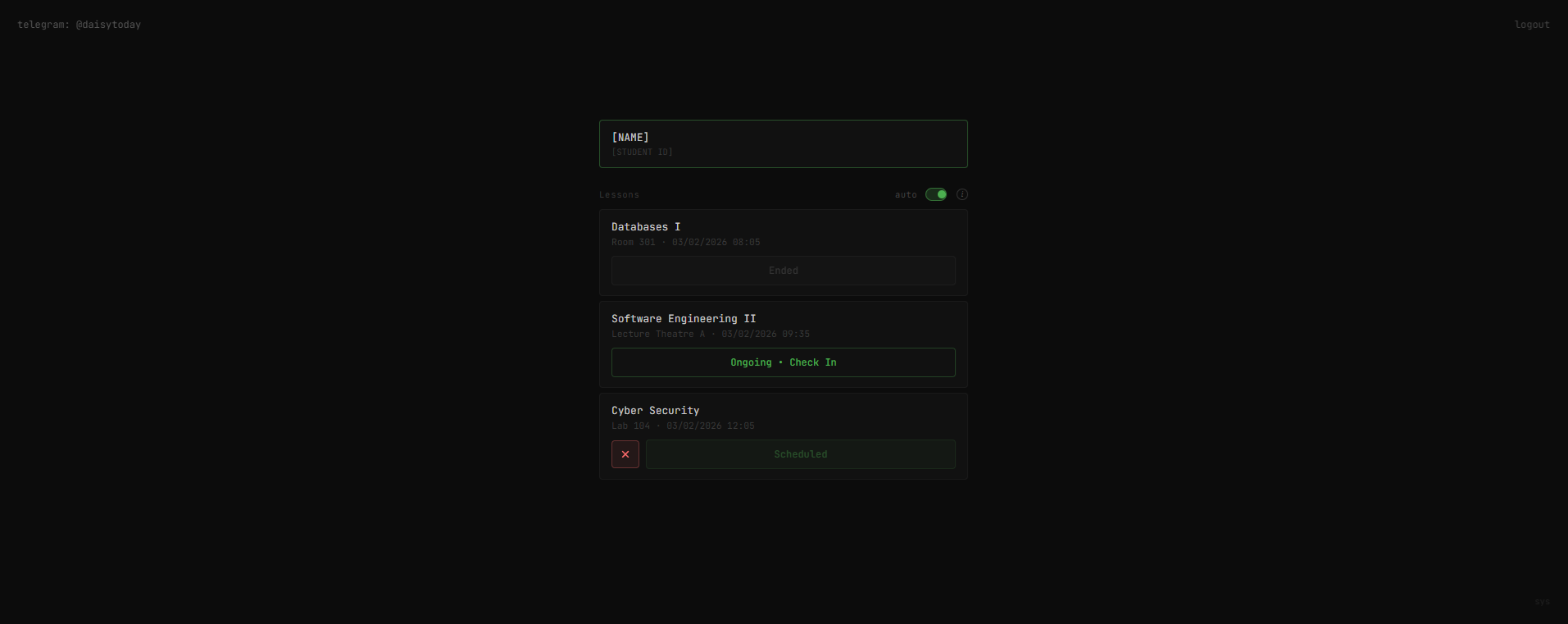
- Auth Isolation - Account security via
PBKDF2hashing. - Chronos-Sync - Server-side event loop polling for offline automation.
- Data Silos - Keyed JSON structures mapping
App ID->Identityto prevent leakage.
Source is no longer public to prevent widespread abuse. Access is restricted to:
- Security Researchers - For peer review and vulnerability analysis.
- SeATS Developers - Reach out if you are finally ready to fix the architecture.
- Verified Devs - Message
@daisytodayon Telegram for clearance.
Educational/Research use only. I don't condone academic dishonesty or bypassing institutional policies. The author assumes no liability for misuse or disciplinary actions. Use at your own risk.
Status: Private Build [v2.1.0-stable]
Origin: @daisytoday