[ETHEREUM-CONTRACTS] allow connecting pools on behalf of members (with some constraints)#2093
Merged
[ETHEREUM-CONTRACTS] allow connecting pools on behalf of members (with some constraints)#2093
Conversation
Signed-off-by: pavedroad <qcqs@outlook.com>
Changelog ReminderReminder to update the CHANGELOG.md for any of the modified packages in this PR.
|
hellwolf
reviewed
Jul 18, 2025
packages/ethereum-contracts/contracts/agreements/gdav1/GeneralDistributionAgreementV1.sol
Outdated
Show resolved
Hide resolved
hellwolf
reviewed
Jul 18, 2025
packages/ethereum-contracts/test/foundry/agreements/gdav1/GeneralDistributionAgreement.t.sol
Outdated
Show resolved
Hide resolved
hellwolf
reviewed
Jul 18, 2025
| cache_path = 'packages/solidity-semantic-money/out/default.cache' | ||
| solc_version = '0.8.26' | ||
| evm_version = 'paris' # no PUSH0 for now | ||
| evm_version = 'paris' |
Contributor
There was a problem hiding this comment.
I will check in a separate PR.
hellwolf
reviewed
Jul 24, 2025
Contributor
There was a problem hiding this comment.
We should make a separate PR for this.
Collaborator
Author
There was a problem hiding this comment.
oh, did I commit this?
Apparently it broke only one line, which I fixed in c5fd4d5. Should it be undone anyway?
hellwolf
reviewed
Jul 24, 2025
packages/ethereum-contracts/contracts/agreements/gdav1/GeneralDistributionAgreementV1.sol
Outdated
Show resolved
Hide resolved
hellwolf
reviewed
Jul 28, 2025
packages/ethereum-contracts/contracts/agreements/gdav1/GeneralDistributionAgreementV1.sol
Outdated
Show resolved
Hide resolved
hellwolf
reviewed
Aug 6, 2025
| // check/set ACL role admins | ||
| const simpleAcl = await SimpleACL.at(simpleAclAddress); | ||
|
|
||
| const aclSuperappRegistrationRoleAdmin = web3.utils.sha3("ACL_SUPERAPP_REGISTRATION_ROLE_ADMIN"); |
hellwolf
approved these changes
Aug 6, 2025
Contributor
|
Suggest for a new PR: Make SimpleACL upgrade robust, by checking if it gets accidentally overriden durign the upgrade process. |
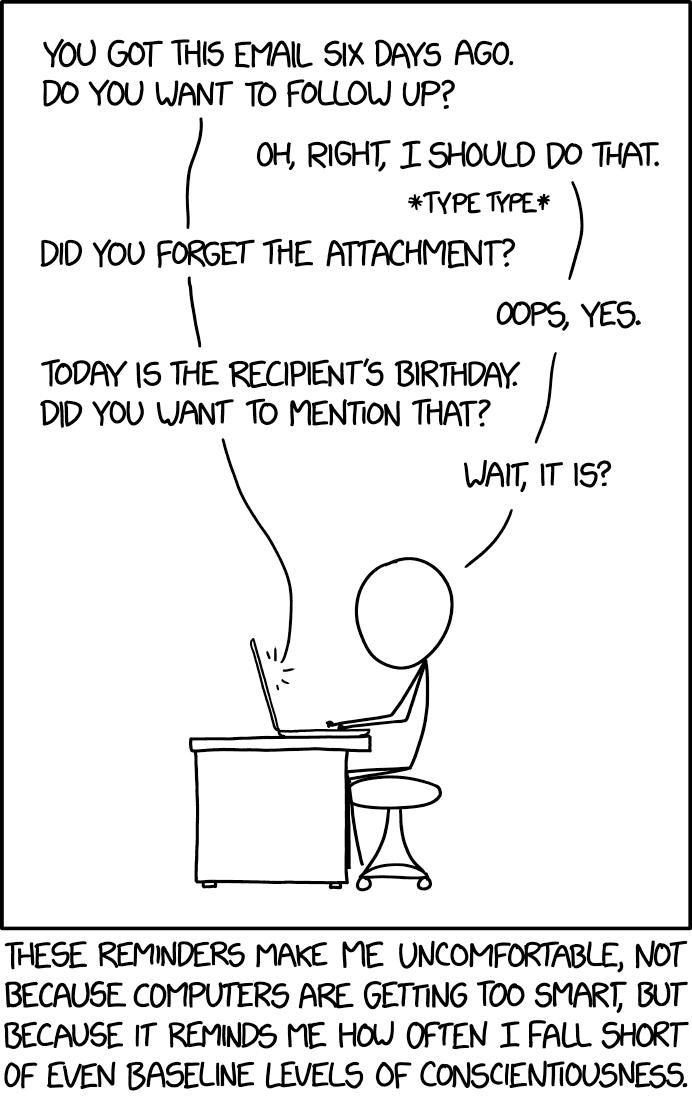
XKCD Comic RelifLink: https://xkcd.com/2093 |
This file contains hidden or bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
Sign up for free
to join this conversation on GitHub.
Already have an account?
Sign in to comment
Add this suggestion to a batch that can be applied as a single commit.This suggestion is invalid because no changes were made to the code.Suggestions cannot be applied while the pull request is closed.Suggestions cannot be applied while viewing a subset of changes.Only one suggestion per line can be applied in a batch.Add this suggestion to a batch that can be applied as a single commit.Applying suggestions on deleted lines is not supported.You must change the existing code in this line in order to create a valid suggestion.Outdated suggestions cannot be applied.This suggestion has been applied or marked resolved.Suggestions cannot be applied from pending reviews.Suggestions cannot be applied on multi-line comments.Suggestions cannot be applied while the pull request is queued to merge.Suggestion cannot be applied right now. Please check back later.
What & Why
Onboarding new users to SuperTokens via GDA distributions is tainted if they have to do a claim transaction before seeing Super Tokens being sent to them.
This can be mitigated by allowing to connect pools on behalf of members.
At the same time this power shall be constraint in order to keep the "spam protection" aspect - 3rd parties shall not be able to use up all slots, and they shall also not be able to increase gas costs for that account due to more expensive balance calculation. Thus autoconnect won't be allowed to use all slots, and a mechanism for accounts to fully opt out will be added.
In short:
How
Add a function to the GDA which allows to connect pools on behalf of members.
Add a mechanism which allows members to opt out of autoconnect.
This can also be viewed as a kind of ACL: by default permission is given, but it can be withdrawn.
Implementation detail:
The pre-existing
connectPoolwill revert if all slots are occupied.The newly added
tryConnectPoolFordoes not revert, but returns a bool signalling if the attempt succeeded.Why not using try/catch: because the gas estimation algorithm of RPC nodes uses binary search to find the smallest gas limit for which the transaction still succeeds, not caring about failing nested calls in try/catch.
TBD
implement a mechanism for a subset of contracts to opt-out of autoconnect by default